5 Best VPN Service 2024
If you are still looking for good vpn to protect your privacy. We recommend you to visit our recommend vpn list below.
| Rank | Provider | Price/Month | Go To Website |
|---|---|---|---|
| 1 |  NordVPN Review | $4.92 |  |
| 2 |  PureVPN Website | $3.33 |  |
| 3 |  Expressvpn Review | $8.32 |  |
| 4 |  Vyprvpn Review | $1.66 |  |
| 5 |  PIA Review | $2.69 |  |
How VPN Works
Double encryption VPN Plus Tor provides the highest level of security and anonymity.
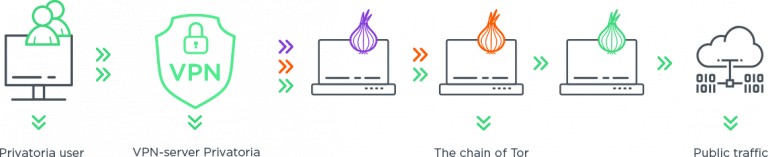
VPN encrypts your traffic and hides your real IP. Tor makes you anonymous routing your traffic through the Tor nodes. No logs
Privatoria VPN + Proxy + Tor
If you are looking for how to unblock blocked websites, how to change IP, how to secure your online traffic, how to download torrents securely, use public WiFi safely, how to use Tor without Tor browser, how to use Tor safely, Privatoria offers a great solution.
Hide IP & encrypt your traffic
Privatoria developed a unique site unblocker solution which hides your real IP address and encrypts your online traffic. Privatoria list of services includes Secure VPN, Anonymous Proxy, Web Proxy Tor, VPN Plus Tor and browser extensions for simple anonymous surfing. VPN Plus Tor and Web Proxy Plus Tor services are unique features which differentiate Privatoria from other VPN providers. Using Privatoria anonymizer you can change IP address and the website you visit doesn’t know who you are and where are you from really. It makes your browser anonymous and opens new opportunities to unblock blocked websites. Privatoria VPN encrypts all your online activities including web browsing and other apps which connect to the Internet from prying eyes. Torrent friendly gateways around the world allow you to enjoy downloading and streaming favorite torrents with high speed.
Zero logs VPN
Your privacy is very important to us. That’s why we have a no logs policy. This means we keep no logs. You can be confident that your confidential information won’t be overheard, intercepted or used against you.
What benefits do you get from anonymous surfing with Privatoria?
Hide & change your real IP address. Encrypt all your traffic and surf from any country in one click. Zero-logs policy. Use Tor without Tor browser. Easy access to dark websites. Get double encryption VPN Plus Tor. Use Tor safely and hide the fact of using Tor from ISP, Tor sees only Privatoria’s VPN IP address. Unblock websites which are not available in your country or blocked by your employer (Facebook, Twitter, YouTube, Netflix, etc…). Make foreign market research from the homeland. Privatoria is a useful tool for market researchers, analytics, product managers, business development managers, SEO specialists, etc… Save your money buying tickets, book hotels and make other online purchases via Proxy to get the cheapest offer. Protect your payments from hackers, encrypt your passwords, credit card details, and other sensitive data online. Use free public WiFi securely, protect your online activity from hackers.
Stay private online with Privatoria.